Rethink & Reboot Deep Packet Inspection from a fixed appliance to a cloud native software tool
Several key revenue threats can affect operator networks, but these are primarily due to users having access to unauthorized services and bypassing existing controls. Accurate deep packet inspection, intelligence and enforcement is the dynamic cloud native software option essential to identify, intercept and block this activity.
Examples of revenue threats from a network perspective:

Domain Fronting
Where a domain appears to be one service but is another in reality. This is a common way for users to access unauthorized content for their plan

SIMBox Fraud
Bypassing interconnect call charges via VOIP routing and local breakout

Unauthorized VPN
Users using VPN apps to bypass content access controls for their plan

Activity Enforcement
A user plan which allows Chat but not VOIP for social network
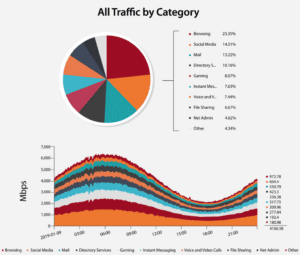
Enea’s cloud native Traffic Classifier DPI solution enables these threats and new risks to be analyzed with thousands of protocol and meta data options.
Traffic Classifier uses the industry leading Enea Qosmos ixEngine as a basis for the widest and most accurate embedded deep packet inspection & classification available today. Qosmos ixEngine is embedded in diverse range of telecom equipment from GGSN to router to firewall; providing a complete view of the traffic path.
- The deep packet inspection and traffic enforcement combines with traffic analytics to provide the dynamic capability to analyze what is happening with application and protocol traffic at multiple levels. The easy to use at GUI enables creation of dynamic traffic queries for key user data generated per flow / session, filtering by multiple vectors including location, time, category, device, protocol on the mobile data access flows.
- The session information and network data provides an extensive set of meta to correlate analysis of consumption, app and protocol.
- Using this sophisticated traffic analysis enables patterns of usage to be better understood, new application changes to be highlighted and any ‘Unknowns’ to be resolved quickly.
Trusted By

More Information